sctf2019-babyre
- ctf
JunkCode + Maze + b64decode + SM4
buuctf 上有价值的题目并不多,这题算是还可以的。
Pass 花指令
IDA 打开,main函数无法解析。
必然存在混淆来干扰分析,直接对main的位置按p创建函数。
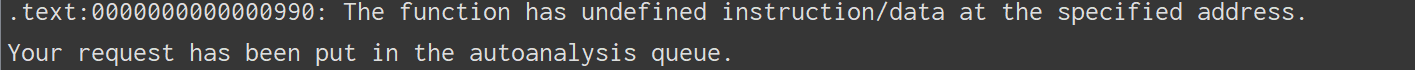
反复操作,nop掉花指令部分。
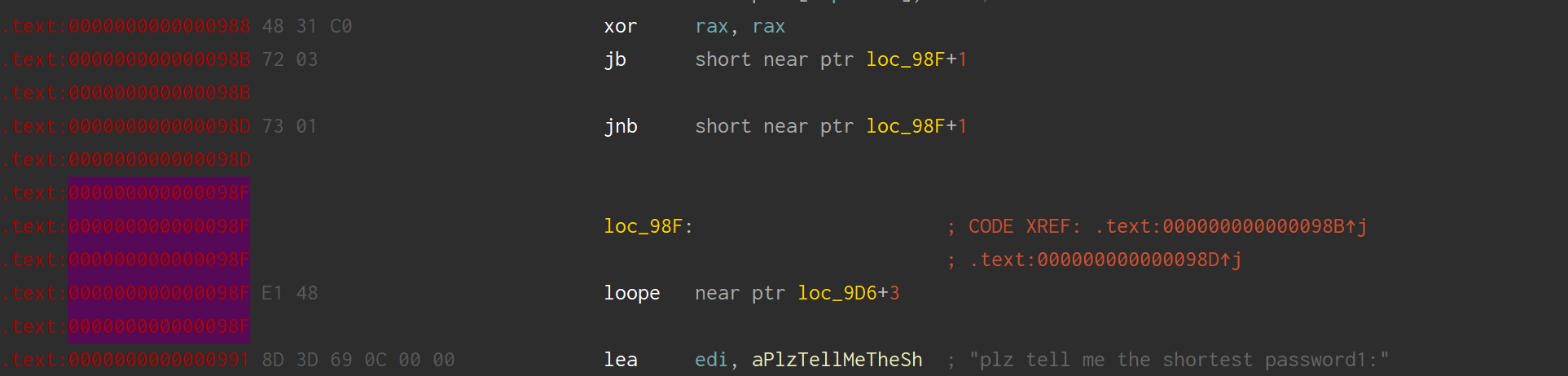
nop掉即可,这样的地方有好几处。
在 LOC22 的位置还有一处比较特别的花
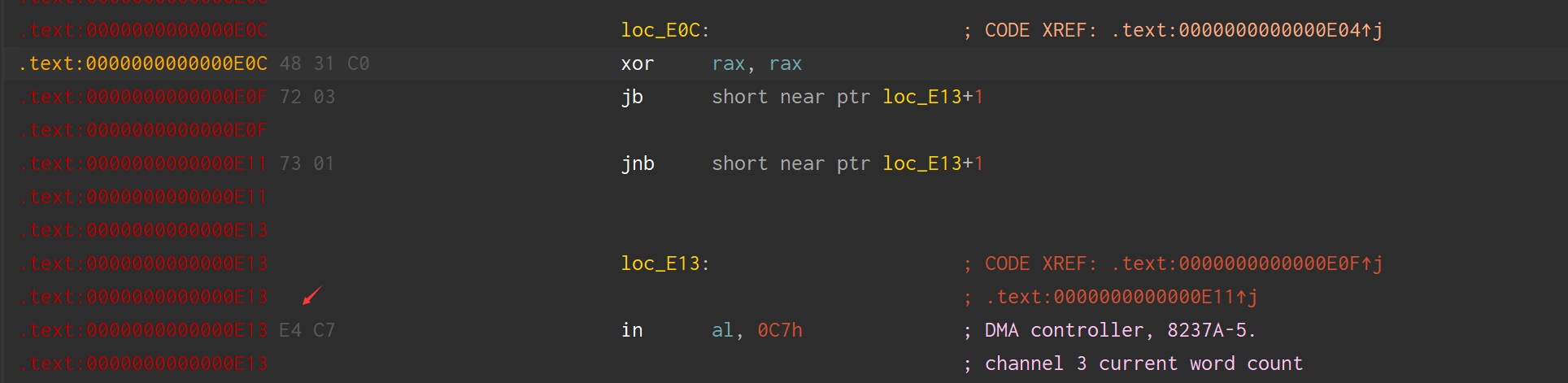
Nop掉 in 指令即可
花指令比较搞人心态,但实际上不是很难。
2. 迷宫
flag_1 部分就是走出这个迷宫,这个迷宫题出的不是很好略过了
正解是 ddwwxxssxaxwwaasasyywwdd,
3. 第一个加密,
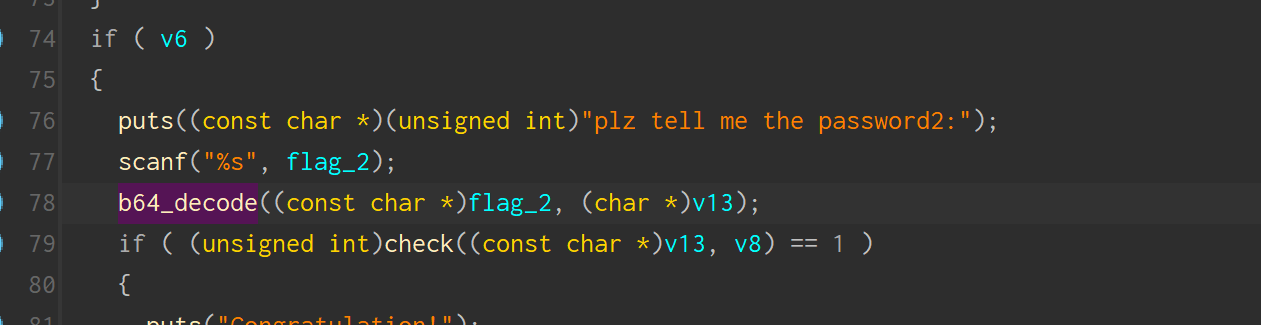
这个函数实际上是 base64 的解密函数
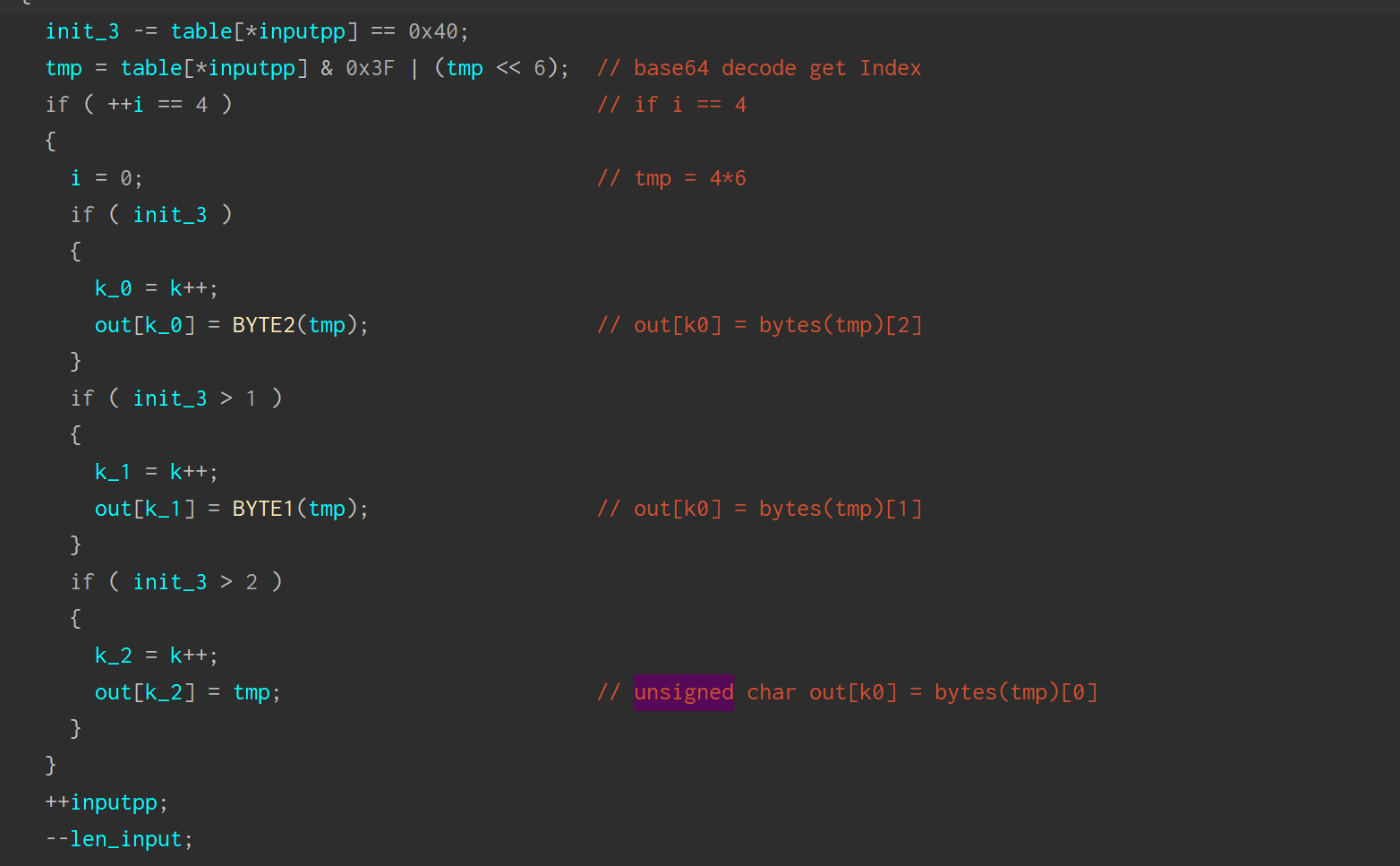
base64 解密的主要特征有这么几个:
- base64 表
- &0x3f <-> &0x0011_1111 ,也就是取6位。然后存在左移 6 位的再
|的操作。实际上这就是把位叠加进行还原。
对于这题来说,这个表被混淆了,或者说魔改了。
table[input[i]],没有那么明显的就是 ABCDE...[input[i]]这种形式,不过无论如何,解密的时候实际上获取的是 CHAR x,x 在 base64 的索引。我们可以用IDAPython把表拿下来。
start = 0x1740
end = 0x1d7f
i = 0
des = []
while i+start<end:
des.append(get_wide_word(start+i))
这样就能得到
des = [0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f,
0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f,
0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x3e, 0x7f, 0x7f, 0x7f, 0x3f, 0x34, 0x35, 0x36, 0x37, 0x38, 0x39, 0x3a, 0x3b,
0x3c, 0x3d, 0x7f, 0x7f, 0x7f, 0x40, 0x7f, 0x7f, 0x7f, 0x0, 0x1, 0x2, 0x3, 0x4, 0x5, 0x6, 0x7, 0x8, 0x9, 0xa, 0xb,
0xc, 0xd, 0xe, 0xf, 0x10, 0x11, 0x12, 0x13, 0x14, 0x15, 0x16, 0x17, 0x18, 0x19, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f,
0x1a, 0x1b, 0x1c, 0x1d, 0x1e, 0x1f, 0x20, 0x21, 0x22, 0x23, 0x24, 0x25, 0x26, 0x27, 0x28, 0x29, 0x2a, 0x2b, 0x2c,
0x2d, 0x2e, 0x2f, 0x30, 0x31, 0x32, 0x33, 0x7f, 0x7f, 0x7f, 0x7f, 0x7f, 0xd6, 0x90, 0xe9, 0xfe, 0xcc, 0xe1, 0x3d,
0xb7, 0x16, 0xb6, 0x14, 0xc2, 0x28, 0xfb, 0x2c, 0x5, 0x2b, 0x67, 0x9a, 0x76, 0x2a, 0xbe, 0x4, 0xc3, 0xaa, 0x44,
0x13, 0x26, 0x49, 0x86, 0x6, 0x99, 0x9c, 0x42, 0x50, 0xf4, 0x91, 0xef, 0x98, 0x7a, 0x33, 0x54, 0xb, 0x43, 0xed,
0xcf, 0xac, 0x62, 0xe4, 0xb3, 0x1c, 0xa9, 0xc9, 0x8, 0xe8, 0x95, 0x80, 0xdf, 0x94, 0xfa, 0x75, 0x8f, 0x3f, 0xa6,
0x47, 0x7, 0xa7, 0xfc, 0xf3, 0x73, 0x17, 0xba, 0x83, 0x59, 0x3c, 0x19, 0xe6, 0x85, 0x4f, 0xa8, 0x68, 0x6b, 0x81,
0xb2, 0x71, 0x64, 0xda, 0x8b, 0xf8, 0xeb, 0xf, 0x4b, 0x70, 0x56, 0x9d, 0x35, 0x1e, 0x24, 0xe, 0x5e, 0x63, 0x58,
0xd1, 0xa2, 0x25, 0x22, 0x7c, 0x3b, 0x1, 0x21, 0x78, 0x87, 0xd4, 0x0, 0x46, 0x57, 0x9f, 0xd3, 0x27, 0x52, 0x4c,
0x36, 0x2, 0xe7, 0xa0, 0xc4, 0xc8, 0x9e, 0xea, 0xbf, 0x8a, 0xd2, 0x40, 0xc7, 0x38, 0xb5, 0xa3, 0xf7, 0xf2, 0xce,
0xf9, 0x61, 0x15, 0xa1, 0xe0, 0xae, 0x5d, 0xa4, 0x9b, 0x34, 0x1a, 0x55, 0xad, 0x93, 0x32, 0x30, 0xf5, 0x8c, 0xb1,
0xe3, 0x1d, 0xf6, 0xe2, 0x2e, 0x82, 0x66, 0xca, 0x60, 0xc0, 0x29, 0x23, 0xab, 0xd, 0x53, 0x4e, 0x6f, 0xd5, 0xdb,
0x37, 0x45, 0xde, 0xfd, 0x8e, 0x2f, 0x3, 0xff, 0x6a, 0x72, 0x6d, 0x6c, 0x5b, 0x51, 0x8d, 0x1b, 0xaf, 0x92, 0xbb,
0xdd, 0xbc, 0x7f, 0x11, 0xd9, 0x5c, 0x41, 0x1f, 0x10, 0x5a, 0xd8, 0xa, 0xc1, 0x31, 0x88, 0xa5, 0xcd, 0x7b, 0xbd,
0x2d, 0x74, 0xd0, 0x12, 0xb8, 0xe5, 0xb4, 0xb0, 0x89, 0x69, 0x97, 0x4a, 0xc, 0x96, 0x77, 0x7e, 0x65, 0xb9, 0xf1,
0x9, 0xc5, 0x6e, 0xc6, 0x84, 0x18, 0xf0, 0x7d, 0xec, 0x3a, 0xdc, 0x4d, 0x20, 0x79, 0xee, 0x5f, 0x3e, 0xd7, 0xcb,
0x39, 0x48, 0xc6, 0xba, 0xb1, 0xa3, 0x50, 0x33, 0xaa, 0x56, 0x97, 0x91, 0x7d, 0x67, 0xdc, 0x22, 0x70, 0xb2]
f = b'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/' for i in f: print(des[i], ',', end='')
然后将正常的表输入进去,得到的输出的确是正常的索引,那么也就意味着,这个查表实际上还是返回的b64 index。
或者我们可以直接手动构造一个 b64加密的字符串,然后调用这里的解密进行观察。
那么flag2就是
import base64
t = 'sctf_9102'
print(base64.b64encode(t.encode()))
# c2N0Zl85MTAy
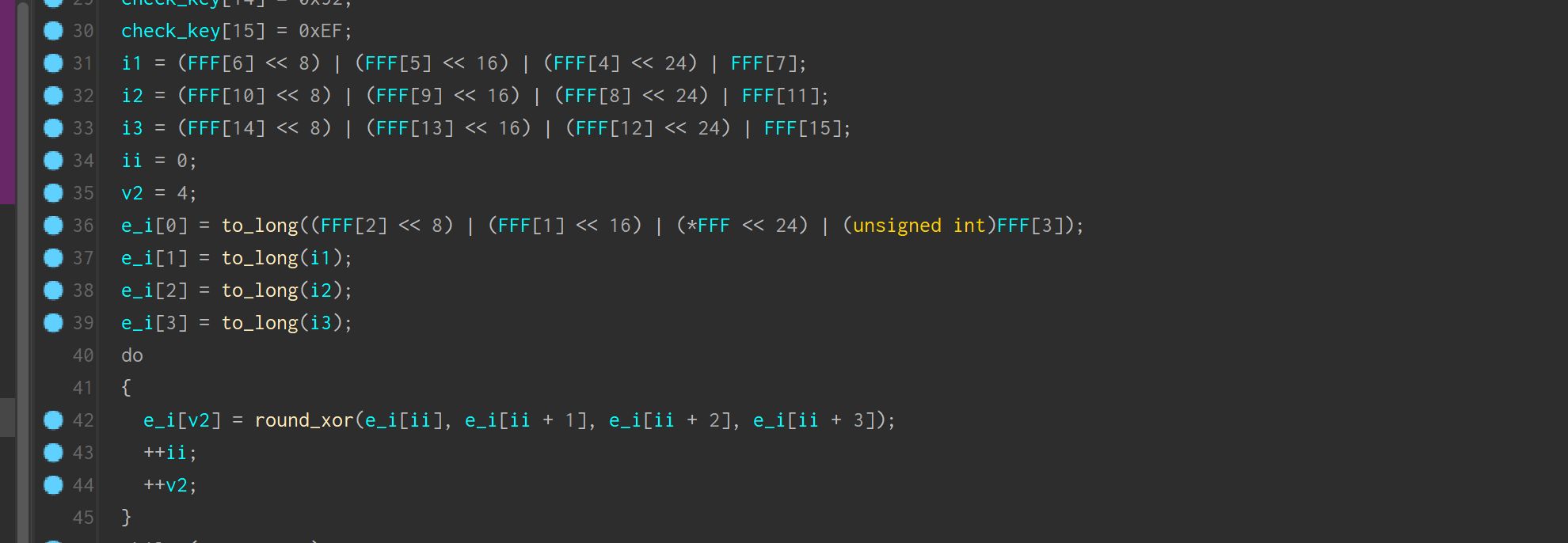
4. 接着是一个阉割的 SM4 加密,主要是阉割了生成密钥轮。
用同样的方法,我们可以拿到S盒
box = [0xd6, 0x90, 0xe9, 0xfe, 0xcc, 0xe1, 0x3d, 0xb7, 0x16, 0xb6, 0x14, 0xc2, 0x28, 0xfb, 0x2c, 0x5, 0x2b, 0x67, 0x9a,
0x76, 0x2a, 0xbe, 0x4, 0xc3, 0xaa, 0x44, 0x13, 0x26, 0x49, 0x86, 0x6, 0x99, 0x9c, 0x42, 0x50, 0xf4, 0x91, 0xef,
0x98, 0x7a, 0x33, 0x54, 0xb, 0x43, 0xed, 0xcf, 0xac, 0x62, 0xe4, 0xb3, 0x1c, 0xa9, 0xc9, 0x8, 0xe8, 0x95, 0x80,
0xdf, 0x94, 0xfa, 0x75, 0x8f, 0x3f, 0xa6, 0x47, 0x7, 0xa7, 0xfc, 0xf3, 0x73, 0x17, 0xba, 0x83, 0x59, 0x3c, 0x19,
0xe6, 0x85, 0x4f, 0xa8, 0x68, 0x6b, 0x81, 0xb2, 0x71, 0x64, 0xda, 0x8b, 0xf8, 0xeb, 0xf, 0x4b, 0x70, 0x56, 0x9d,
0x35, 0x1e, 0x24, 0xe, 0x5e, 0x63, 0x58, 0xd1, 0xa2, 0x25, 0x22, 0x7c, 0x3b, 0x1, 0x21, 0x78, 0x87, 0xd4, 0x0,
0x46, 0x57, 0x9f, 0xd3, 0x27, 0x52, 0x4c, 0x36, 0x2, 0xe7, 0xa0, 0xc4, 0xc8, 0x9e, 0xea, 0xbf, 0x8a, 0xd2, 0x40,
0xc7, 0x38, 0xb5, 0xa3, 0xf7, 0xf2, 0xce, 0xf9, 0x61, 0x15, 0xa1, 0xe0, 0xae, 0x5d, 0xa4, 0x9b, 0x34, 0x1a, 0x55,
0xad, 0x93, 0x32, 0x30, 0xf5, 0x8c, 0xb1, 0xe3, 0x1d, 0xf6, 0xe2, 0x2e, 0x82, 0x66, 0xca, 0x60, 0xc0, 0x29, 0x23,
0xab, 0xd, 0x53, 0x4e, 0x6f, 0xd5, 0xdb, 0x37, 0x45, 0xde, 0xfd, 0x8e, 0x2f, 0x3, 0xff, 0x6a, 0x72, 0x6d, 0x6c,
0x5b, 0x51, 0x8d, 0x1b, 0xaf, 0x92, 0xbb, 0xdd, 0xbc, 0x7f, 0x11, 0xd9, 0x5c, 0x41, 0x1f, 0x10, 0x5a, 0xd8, 0xa,
0xc1, 0x31, 0x88, 0xa5, 0xcd, 0x7b, 0xbd, 0x2d, 0x74, 0xd0, 0x12, 0xb8, 0xe5, 0xb4, 0xb0, 0x89, 0x69, 0x97, 0x4a,
0xc, 0x96, 0x77, 0x7e, 0x65, 0xb9, 0xf1, 0x9, 0xc5, 0x6e, 0xc6, 0x84, 0x18, 0xf0, 0x7d, 0xec, 0x3a, 0xdc, 0x4d,
0x20, 0x79, 0xee, 0x5f, 0x3e, 0xd7, 0xcb, 0x39, 0x48, 0xc6, 0xba, 0xb1, 0xa3, 0x50, 0x33, 0xaa, 0x56, 0x97, 0x91,
0x7d, 0x67, 0xdc, 0x22, 0x70, 0xb2]
加密过程大概如下:
init:
arr[0..3] = input[0..3]–>bytes
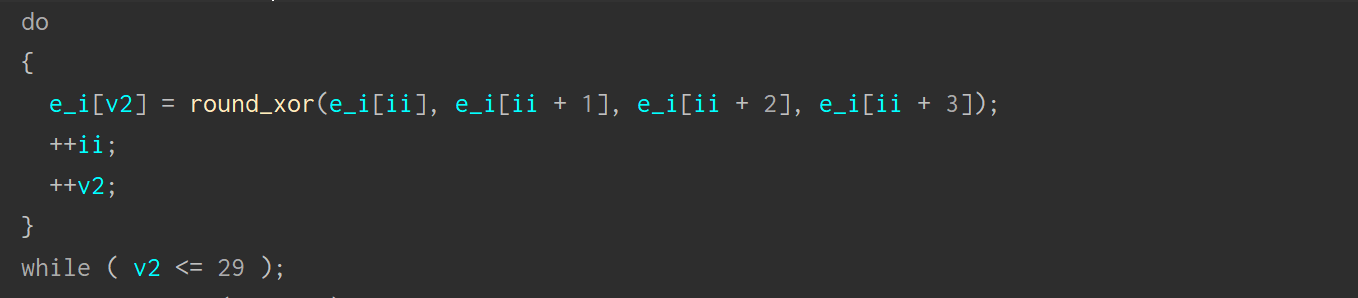
arr[i] = arr[i-4] ^ S_BOX_Change(arr[i-3] ^ arr[i-2] ^ arr[i-1])
题目加密了 30 轮
这个等式,两边同时异或 S_BOX[T]
arr[i] ^ S[T] = arr[i-4]
–> arr[i] = arr[i+4] ^ S_B_C(arr[i+1] ^ arr[i+2] ^ arr[i+1])
我们已知 a29,a28,a27,a26
那么 a25 = a29 ^ S_B_C(a28 ^ a27 ^ a26)
后面四个量都是已知的,就可以依次逆推到a0,a1,a2,a3。
那么我们只要把 S 盒的变化实现就可以逆推。
加密部分如下:
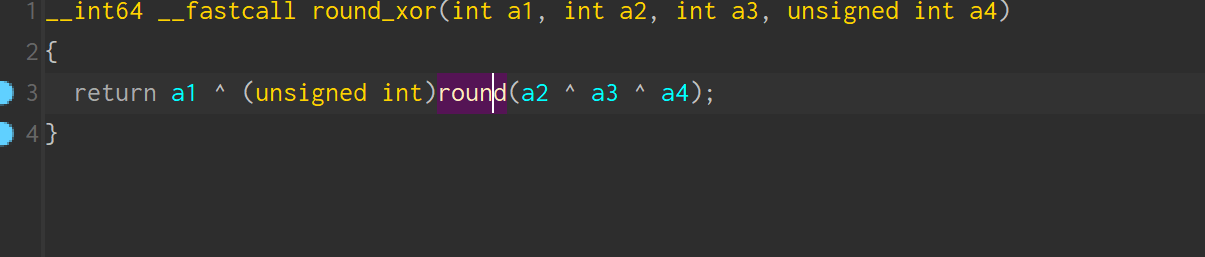
着重分析的就是里面这个函数
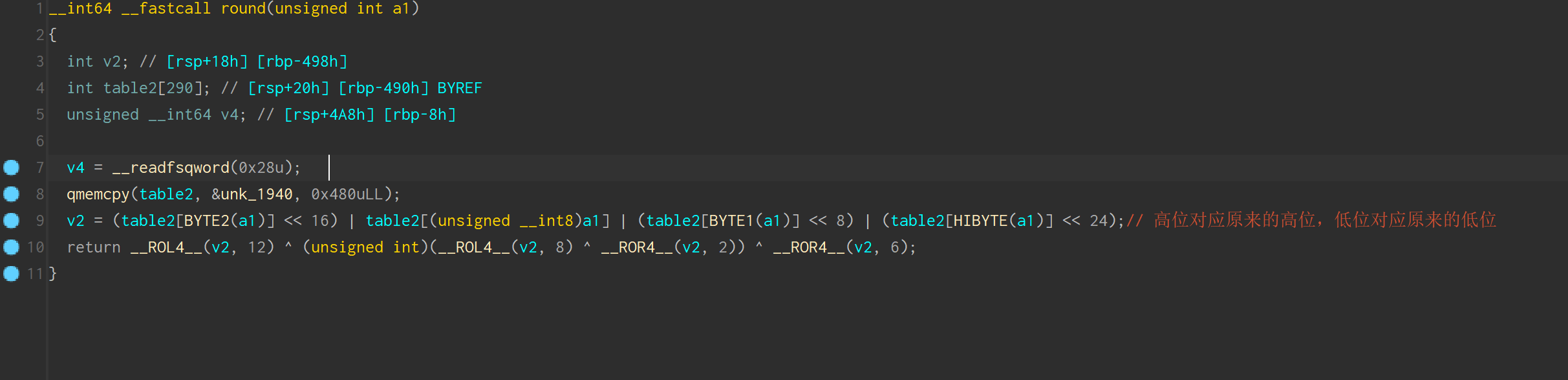
那么这里table对应的就是S盒,v2 的值实际上就是 a1(三个数异或的结果)分成4*8bits的形式。
逻辑左移,右端补0。
a1 分成四组,用数字代表每组的相对位置,实际上这些数只能是0或1
44444444 33333333 22222222 11111111
high —————————low
左边是高位,右边是低位。
Byte2(a1) ,实际上是取了 3 的那8位,Byte1 是2 ,直接读 8 位,会截断,也就是1,HIByte 也就是 4. 那么位移之后再或运算,实际上就还原了这个数,而这里分组,实际上就是进行 S 盒变换。
S 盒 变换之后,再进行逻辑左移 异或的 操作。
我们只要实现这些逻辑反着迭代就可以得到flag了,这个脚本参考了另外一个csdn上的博主,左移2位等于右移30位。
box = [0xd6, 0x90, 0xe9, 0xfe, 0xcc, 0xe1, 0x3d, 0xb7, 0x16, 0xb6, 0x14, 0xc2, 0x28, 0xfb, 0x2c, 0x5, 0x2b, 0x67, 0x9a,
0x76, 0x2a, 0xbe, 0x4, 0xc3, 0xaa, 0x44, 0x13, 0x26, 0x49, 0x86, 0x6, 0x99, 0x9c, 0x42, 0x50, 0xf4, 0x91, 0xef,
0x98, 0x7a, 0x33, 0x54, 0xb, 0x43, 0xed, 0xcf, 0xac, 0x62, 0xe4, 0xb3, 0x1c, 0xa9, 0xc9, 0x8, 0xe8, 0x95, 0x80,
0xdf, 0x94, 0xfa, 0x75, 0x8f, 0x3f, 0xa6, 0x47, 0x7, 0xa7, 0xfc, 0xf3, 0x73, 0x17, 0xba, 0x83, 0x59, 0x3c, 0x19,
0xe6, 0x85, 0x4f, 0xa8, 0x68, 0x6b, 0x81, 0xb2, 0x71, 0x64, 0xda, 0x8b, 0xf8, 0xeb, 0xf, 0x4b, 0x70, 0x56, 0x9d,
0x35, 0x1e, 0x24, 0xe, 0x5e, 0x63, 0x58, 0xd1, 0xa2, 0x25, 0x22, 0x7c, 0x3b, 0x1, 0x21, 0x78, 0x87, 0xd4, 0x0,
0x46, 0x57, 0x9f, 0xd3, 0x27, 0x52, 0x4c, 0x36, 0x2, 0xe7, 0xa0, 0xc4, 0xc8, 0x9e, 0xea, 0xbf, 0x8a, 0xd2, 0x40,
0xc7, 0x38, 0xb5, 0xa3, 0xf7, 0xf2, 0xce, 0xf9, 0x61, 0x15, 0xa1, 0xe0, 0xae, 0x5d, 0xa4, 0x9b, 0x34, 0x1a, 0x55,
0xad, 0x93, 0x32, 0x30, 0xf5, 0x8c, 0xb1, 0xe3, 0x1d, 0xf6, 0xe2, 0x2e, 0x82, 0x66, 0xca, 0x60, 0xc0, 0x29, 0x23,
0xab, 0xd, 0x53, 0x4e, 0x6f, 0xd5, 0xdb, 0x37, 0x45, 0xde, 0xfd, 0x8e, 0x2f, 0x3, 0xff, 0x6a, 0x72, 0x6d, 0x6c,
0x5b, 0x51, 0x8d, 0x1b, 0xaf, 0x92, 0xbb, 0xdd, 0xbc, 0x7f, 0x11, 0xd9, 0x5c, 0x41, 0x1f, 0x10, 0x5a, 0xd8, 0xa,
0xc1, 0x31, 0x88, 0xa5, 0xcd, 0x7b, 0xbd, 0x2d, 0x74, 0xd0, 0x12, 0xb8, 0xe5, 0xb4, 0xb0, 0x89, 0x69, 0x97, 0x4a,
0xc, 0x96, 0x77, 0x7e, 0x65, 0xb9, 0xf1, 0x9, 0xc5, 0x6e, 0xc6, 0x84, 0x18, 0xf0, 0x7d, 0xec, 0x3a, 0xdc, 0x4d,
0x20, 0x79, 0xee, 0x5f, 0x3e, 0xd7, 0xcb, 0x39, 0x48, 0xc6, 0xba, 0xb1, 0xa3, 0x50, 0x33, 0xaa, 0x56, 0x97, 0x91,
0x7d, 0x67, 0xdc, 0x22, 0x70, 0xb2]
def rol(i, n):
return (i >> (32 - n) | (i << n)) & 0xFFFFFFFF
def s_box(i: int):
res = bytearray()
i = i.to_bytes(4, 'big')
for j in i:
res.append(box[j])
return int.from_bytes(res, 'big')
out = [0 for _ in range(30)]
out[29] = 0xd8bf92ef
out[28] = 0x9fcc401f
out[27] = 0xc5af7647
out[26] = 0xbe040680
i = 25
while i > -1:
box_in = out[i + 1] ^ out[i + 2] ^ out[i + 3]
box_out = s_box(box_in)
out[i] = out[i + 4] ^ rol(box_out, 12) ^ rol(box_out, 8) ^ rol(box_out, 30) ^ rol(box_out, 26)
i -= 1
s3 = b''
for i in range(4):
s3 += out[i].to_bytes(4, 'little')
print(s3)
得到flag3
fl4g_is_s0_ug1y!